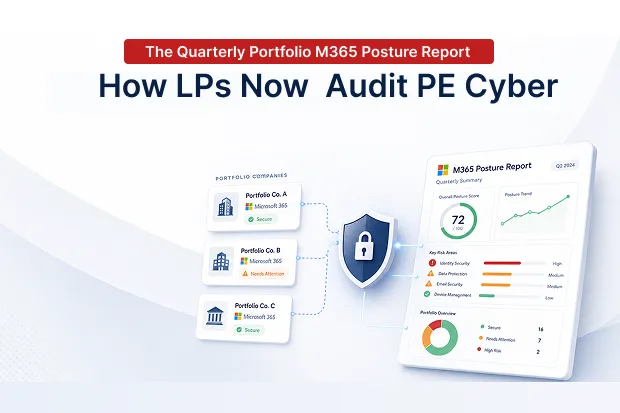
There is an important conversation happening in private equity today that was not common five years ago. Limited Partners (LPs), such as pension funds, sovereign wealth funds, endowments, and insurance companies, no longer accept simple statements like “our portfolio companies take cybersecurity seriously.” They now want clear numbers and measurable data every quarter across all portfolio companies (PortCos) in a format that is easy to compare.
If you are a GP, fund-level CISO, or Operating Partner preparing reports for LP updates, you already know that quarterly Microsoft 365 security posture reporting has become a major part of modern private equity operations.
One statistic changed LP expectations significantly:
55% of PE firms with more than $2.5B in AUM now require a mandatory cybersecurity baseline across their portfolio companies. In comparison, only 12% of firms below $2.5B do the same.
If a private equity firm has 10 to 50 portfolio companies (PortCos), the overall cybersecurity safety of the entire portfolio is not determined by the strongest company, but by the weakest one.
So even if 49 companies are secure, one weak company can still create a major risk for the whole portfolio. That’s why LPs now want to see not just the average security score, but the full spread of security performance across the entire portfolio.
- Why LPs Are Getting Involved Now
- What Actually Goes Into the Report
- The High-Stakes Moment: Operational Due Diligence During a Fund Raise
- The Aggregation Problem Nobody Wants to Own
- When an Incident Happens: The Materiality Question
- The Continuation Vehicle Conversation Nobody Wants
- Writing a Report That Builds Trust
- What the Report Is Really Defending
Why LPs Are Getting Involved Now
For many years, cybersecurity stayed in the background during LP discussions. It was seen as just another risk area, not something that needed detailed reporting. That changed when the evidence became too serious to ignore.
According to Kroll’s February 2026 survey of 325 private equity leaders, 80% of firms experienced business disruption linked to cybersecurity problems during the holding period in the past year. Around 70% said the problem has become worse year after year. Even more importantly, 26% of firms reported that cyber incidents directly reduced company valuation or lowered exit prices.
When LPs see numbers like these, the conversation changes quickly. Instead of asking general questions about cybersecurity, they now ask: “What are you doing about it every quarter?”
The pressure also comes from regulators overseeing the LPs themselves. Public pension funds, sovereign wealth funds, and large insurance firms must show that their alternative investments are not building hidden cyber risk. Because of that, LPs ask GPs for proof, and GPs then need answers from every portfolio company.
The challenge is that cybersecurity maturity is usually very different across a portfolio. About 52% of large PE firms have a dedicated fund-level CISO, while only 15% of smaller firms do. LPs often look at this gap first when evaluating how seriously a PE firm manages cyber risk.
What Actually Goes Into the Report
The quarterly report is not just a written explanation or a reassuring note in a GP letter. It is a structured data report, and its main parts have now become fairly standard and predictable.
- Portfolio-wide M365 Secure Score, aggregated across every PortCo tenant, with quarter-over-quarter change
- MFA coverage – 100% on admin accounts and industry-standard 95%+ on standard users
- Conditional Access policy maturity and baseline conformance, PortCo by PortCo
- Sensitivity label deployment, retention policy alignment, and audit log retention status
- Incidents during the quarter, with severity and disclosure status
- Cyber insurance coverage, renewal status, and any underwriter findings worth flagging
- eDiscovery hold inventory health and privileged access governance posture
Secure Score has become a key metric because Microsoft allows it to be compared consistently across tenants. That comparability is why many PE firms now include minimum Secure Score requirements directly in their term sheets.
(For the deal-economics side of Secure Score, see our companion piece on M365 Secure Score as a term-sheet adjuster
The High-Stakes Moment: Operational Due Diligence During a Fund Raise
Quarterly reporting is the normal process. The real pressure comes when raising a new fund.
Institutional LPs now regularly check the cybersecurity posture of the existing portfolio during Operational Due Diligence (ODD). Their review can directly affect investment decisions. ODD teams usually ask for proof such as security baseline enforcement, portfolio incident history, fund-level CISO structure, Secure Score distribution across portfolio companies, and how quickly security issues are fixed. They do not want simple yes/no answers, they expect real evidence and reports.
If the cybersecurity posture looks weak, fundraising can be delayed by three to six months, total committed capital may fall below target, and some LPs may avoid investing in certain assets within the fund.
The best way to avoid these problems is to prepare early by running a cyber-readiness audit across the portfolio before fundraising starts, along with a clear remediation plan for unresolved issues. This helps the firm answer ODD questions confidently instead of reacting at the last minute.
The Aggregation Problem Nobody Wants to Own
Combining Secure Score data from 10 to 50 portfolio company (PortCo) tenants may sound easy, but it is actually difficult.
Microsoft Lighthouse was designed for MSPs managing external customers, not for PE firms managing their own portfolio companies. Manual tracking through spreadsheets is unreliable and can break when a PortCo changes its admin team. Microsoft also does not provide a native tool built for LP-style reporting across a PE portfolio.
Because of this, fund-level CISOs are asking for a dashboard designed specifically for PE firms, one that can manage 10–50 tenants, create clean reports for LPs, and easily track changes between reporting periods instead of turning quarterly reporting into a manual headache.
When an Incident Happens: The Materiality Question
When a portfolio company (PortCo) faces a cyber incident, the biggest question becomes whether the incident must be disclosed or not.
Public PortCos must follow SEC rules and report major cyber incidents within four business days using Form 8-K. Private PortCos also face disclosure requirements through agreements such as SPA terms, loan agreements, cyber insurance policies, and LP side letters.
Making the wrong decision can create problems. Reporting too much may damage reputation and market confidence unnecessarily. Reporting too little may lead to regulatory action or legal issues.
The best approach is to prepare a clear disclosure decision process before an incident happens. This should be planned separately for each PortCo, together with legal advisors, insurance providers, and LP representatives, and supported by a fast incident response process that can meet reporting deadlines.
The Continuation Vehicle Conversation Nobody Wants
If cybersecurity governance is weak, a company’s valuation may fall, making it difficult for the fund to exit at a good price. In that situation, the GP may move the asset into a continuation vehicle (CV) structure with new LP investors and extend the holding period.
If Microsoft 365 security gaps were known for years but not fixed, LPs may question the GP’s decisions.
The best protection is to document M365 governance improvements every quarter and openly disclose security gaps and remediation plans during the annual portfolio review.
Writing a Report That Builds Trust
There is a natural tendency to make cybersecurity reports look better than reality, but that approach can create problems later.
If a report hides security gaps, LPs may trust the firm at first. But if a cyber incident later exposes the hidden problems, that trust can disappear quickly. On the other hand, reporting every small issue can create unnecessary concern and make future fundraising harder.
The best approach is balanced and honest reporting based on a clear security baseline that is actually enforced, not just recommended.
For PE firms with less than $2.5B AUM that cannot afford a full-time fund-level CISO, there are practical alternatives such as fractional CISO services, shared MSP arrangements, and PE-focused portfolio security dashboards.
What the Report Is Really Defending
At the fund level, the quarterly Microsoft 365 security posture report helps protect four important areas:
- Trust and credibility when LPs review the fund during Operational Due Diligence (ODD) for the next fundraising cycle
- Company exit valuation, since many PE firms have already faced lower valuations because of cybersecurity issues
- Cyber insurance costs, because a standardized security approach across the portfolio can reduce insurance premiums by 20–40%
- The GP’s ability to defend their decisions if a continuation vehicle (CV) is later proposed and LPs question past cybersecurity management
The quarterly report is not just extra administrative work. It turns Microsoft 365 security posture into something LPs can evaluate, GPs can defend, and fund-level CISOs can actively manage across the portfolio. That is why it has quietly become standard practice for PE firms preparing to raise future funds smoothly.
Related reading: