Your organization is six weeks from closing an acquisition. Legal has reviewed contracts, finance has modelled synergies, and IT has scoped the Microsoft 365 tenant to tenant migration.
The migration plan covers Exchange, Teams, SharePoint, OneDrive, and Power Platform.
What it doesn’t cover is most SaaS applications that IT has never inventoried.
In reality, every enterprise acquires not just a tenant; it acquires an entire shadow technology ecosystem that no one mapped during due diligence.
When that ecosystem collides with the acquiring organization’s security posture, compliance requirements, and integration timeline, the consequences aren’t helpdesk tickets. They’re regulatory exposure, data breaches, and integration delays that erode deal value.
Discovering shadow IT during DD before signing?
See our companion guides – The Pre-Deal M365 Due Diligence Pillar and – for the complete pre-deal discovery framework.
- The Scale of What You Don’t Know
- Why Traditional M&A Due Diligence Misses Shadow IT
- What Breaks During Tenant Migration When Shadow IT Is Unaccounted For
- The Five Categories of Shadow IT Risk in M&A
- CTO/IT Manager Inventory Playbook — Run These Now
- Method 1: Entra ID Enterprise Applications (60–80% Coverage, Zero Cost)
- The Organizational Consequences of Getting This Wrong
- What This Means for Your Migration Plan
The Scale of What You Don’t Know
The gap between what IT manages and what employees use has grown into one of the most significant blind spots in M&A technology due diligence.
Industry studies indicate that the majority of enterprise SaaS usage operates outside formal IT governance.
Industry research indicates that large enterprises with more than 10,000 employees use over 1,400 SaaS applications, while IT teams typically manage only 10–15% of them
The rest operate outside governance, procurement oversight, and security review.
Analysts at Gartner estimate that shadow IT accounts for 30–40% of total IT spending in large enterprises, translating to millions of dollars spent on technology that security and compliance teams may not even know exists.
Recent industry data shows that employees now use an average of 13 SaaS tools each, up from 7 in 2022, an 85% increase in just two years.
In a single-company context, this is a governance and cost problem. In an M&A context, it becomes an integration risk multiplier. Every unmanaged application in the acquired company represents a potential data flow you can’t map, a compliance obligation you can’t verify, and an integration dependency you can’t plan for.
Why Traditional M&A Due Diligence Misses Shadow IT
M&A technology due diligence typically follows a structured process: review the IT asset register, examine vendor contracts, audit the Microsoft 365 tenant, assess the security posture.
The problem is that this process examines what IT knows about.
Shadow IT exists precisely because IT doesn’t know about it.
As a result, traditional due diligence often produces a complete assessment of an incomplete environment.
The inventory gap
When an acquiring company asks, “What applications does your organization use?”, the answer typically comes from IT-controlled systems:
- Configuration management databases (CMDB)
- Procurement records
- SSO or identity provider logs
These sources capture the known cloud services. They miss the unknown ones.
Department leaders may approve tools using corporate credit cards. Individual employees sign up for freemium services using their work email addresses. Teams adopt collaboration or productivity platforms to solve immediate operational problems without going through procurement or IT review.
Marketing may run campaign analytics on a SaaS platform finance has never seen. Engineering teams may operate CI/CD pipelines connected to external APIs that never appear in any vendor register.
None of these tools appear in the due diligence data room.
Yet many of them support real business processes that the migration will inevitably impact
For the exact SaaS discovery artifacts, OAuth consent exports, and non-human identity registers you should demand from the seller, see .
The non-human identity blind spot
Beyond human users, every SaaS application creates non-human identities such as service accounts, API keys, OAuth tokens, automation credentials, that enable system-to-system communication.
Industry research and enterprise audits indicate that non-human identities such as service accounts, API keys, and automation credentials can outnumber human users by as much as 45 to 1 in complex environments..
During an M&A, the convergence of two technology ecosystems compounds this risk. The acquired company may have:
- Service principals connected to third-party applications that IT never provisioned
- Automation scripts running with elevated privileges under accounts tied to employees who have already left
- API keys and tokens that persist indefinitely, providing backdoor access to critical systems long after the M&A closes
- Machine identities provisioned by AI agents and automation platforms that no one tracks or governs
A single orphaned service account in the acquired tenant can provide an attacker with a direct entry point into the merged environment.
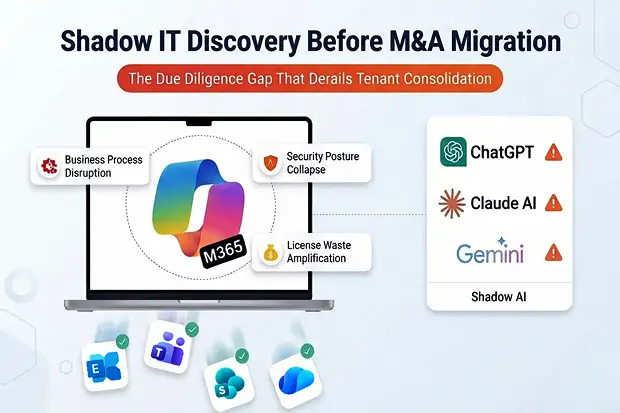
The shadow AI dimension
The latest evolution of shadow IT is shadow AI.
Industry surveys show that a majority of cybersecurity leaders acknowledge employees are using unauthorized AI tools inside their organizations.
Additionally, over half of third-party SaaS vendors now include embedded AI features, often activated by default, which may process sensitive corporate data without IT oversight.
Employees use personal ChatGPT accounts for work tasks, activate AI features embedded in SaaS platforms, and adopt AI-powered productivity tools, often without IT awareness or oversight.
In an M&A context, shadow AI creates risks that traditional due diligence doesn’t even know to ask about:
- Data exposure: Employees may have uploaded sensitive corporate data, financial models, customer lists, strategic plans into AI platforms that retain training data
- IP contamination: AI-generated content may introduce intellectual property uncertainties that affect the deal’s value proposition
- Regulatory gaps: AI tools processing personal data may violate GDPR, CCPA, or industry-specific regulations without anyone’s knowledge
- Post-close remediation cost: If shadow AI usage is discovered after the deal closes, remediation efforts can take 30–90 days or more, delaying integration timelines and expected synergies.
What Breaks During Tenant Migration When Shadow IT Is Unaccounted For
Shadow IT doesn’t just create a due diligence gap. It creates cascading failures during the actual tenant-to-tenant migration that no migration tool can anticipate.
Business process disruption
When a department in the acquired company runs a critical workflow on an unmanaged SaaS platform, migration can break that workflow without warning. For example, an operations team using a project management tool integrated with Microsoft 365 via OAuth, the migration can sever that connection without warning. The OAuth tokens reference the source tenant’s Entra ID. Once users are migrated to the target tenant, those tokens become invalid. The SaaS application stops receiving data. The workflow breaks.
This scenario occurs frequently during tenant consolidations. Power Platform alone is frequently described as the “invisible risk” in M&A. When shadow Power Automate flows built by business users outside IT governance lose their connections during migration, approvals stop arriving, notifications fail, and integrations break silently. If unmanaged SaaS tools feed into or receive from these flows, the blast radius expands beyond what the migration team can diagnose.
Security posture collapse
The acquiring company has spent years building its security posture: Conditional Access policies, DLP rules, Defender for Cloud Apps configurations, sensitivity labels. The acquired company’s shadow IT bypasses all of it.
When users from the acquired company are migrated into the target tenant, they bring their shadow IT habits with them. They continue using unsanctioned applications, but now those applications are connecting to the acquirer’s tenant, a tenant with different DLP policies, different Conditional Access rules, and different data classification standards. The result is a compliance gap that may not surface until an audit, a breach, or a regulatory inquiry.
License waste amplification
Industry analysis shows that shadow IT generates billions in yearly licensing waste from unused and duplicate subscriptions in large enterprises. In an M&A, this problem doubles. Both organizations carry their own shadow SaaS portfolios, many of which overlap. Without discovery, the merged entity pays for two instances of the same tool across departments, neither of which IT manages or can rationalize.
For an enterprise already absorbing significant duplicate Microsoft 365 licensing costs during the coexistence period, adding unquantified shadow SaaS costs on top transforms what should be a migration cost into an ongoing financial leak that no one has budgeted for.
The Five Categories of Shadow IT Risk in M&A
Not all shadow IT carries the same risk profile during an M&A migration. Understanding the categories helps prioritize discovery and remediation.
1. Data-bearing shadow SaaS
Applications where employees have stored, processed, or shared corporate data. This includes file storage services, project management platforms, CRM alternatives, and communication tools. These carry the highest compliance risk because the data may include customer PII, financial records, or regulated information that the acquiring company is now responsible for.
2. Identity-connected shadow SaaS
Applications that authenticate via Microsoft Entra ID (through OAuth or SAML), even if IT never approved them. These create Entra ID application registrations and service principals in the source tenant. During migration, these registrations don’t transfer. The SaaS applications lose authentication. Business users lose access to tools they depend on, and IT doesn’t know the tools exist to fix them.
3. Integration-dependent shadow SaaS
Applications connected to Microsoft 365 workloads through APIs, connectors, or webhooks. A marketing automation platform pulling data from SharePoint lists. A finance tool syncing with Excel files in OneDrive. An HR system connected to Entra ID for identity lifecycle management. These integrations break silently during migration because they reference source tenant endpoints that no longer resolve.
4. Shadow automation (Power Platform and beyond)
Business users build automations such as Power Automate flows, Power Apps, Logic Apps that connect Microsoft 365 to external services. These automations run under individual user accounts, use personal connections, and are invisible to IT unless specifically inventoried. In an M&A, every one of these automations is a potential silent failure point.
5. Shadow AI and generative tools
The newest category, and the one least likely to appear in any inventory. Personal AI accounts used for work, AI features embedded in SaaS platforms, browser extensions with AI capabilities. These tools may have ingested sensitive data from the acquired company that now represents a liability for the acquiring organization.
CTO/IT Manager Inventory Playbook — Run These Now
As a CTO or IT Manager, here is your actionable playbook to inventory SaaS applications in the tenant. This combines native Microsoft tools with the most effective third-party approaches.
Method 1: Entra ID Enterprise Applications (60–80% Coverage, Zero Cost)
Every OAuth or SAML consent creates an “Enterprise Application” (service principal) in Entra ID. Auditing these catches 60–80% of identity-connected shadow IT, according to Microsoft’s Defender for Cloud Apps documentation.
How to run it:
Use the Microsoft Graph PowerShell module to export all service principals from the tenant:
- Connect to your tenant using Connect-MgGraph with Application.Read.All and Directory.Read.All scopes
- Retrieve all service principals using Get-MgServicePrincipal -All
- Filter out Microsoft first-party applications (publisher name containing “Microsoft Corporation” or “Microsoft Services”)
- Filter out well-known Microsoft app names (Windows, Office, Teams, SharePoint, OneDrive, Outlook, Exchange, Power*, Dynamics)
- Sort the remaining applications by creation date (newest first, recently created apps are higher risk)
- For each remaining app, retrieve the owner using Get-MgServicePrincipalOwner to identify who authorized it
- Export to Excel for review
What to look for in the results:
- Applications with no identifiable owner (orphaned apps)
- Applications created in the last 30 days (may have been set up hastily before the deal)
- Applications with broad permissions (Directory.ReadWrite.All, Mail.ReadWrite, Files.ReadWrite.All)
- Applications you don’t recognize, these are your shadow IT candidates
Expected output: 50–200 shadow application candidates on first run in most enterprises.
Method 2: Defender for Cloud Apps — Cloud Discovery (90%+ Coverage)
This requires a Microsoft 365 E5 license or Defender for Endpoint combined with Defender for Cloud Apps license.
Setup (approximately 10 minutes):
- Navigate to Defender for Cloud Apps, then Cloud Discovery, then Discovery settings
- Enable “Automatic log upload” from Defender for Endpoint
- Wait 24–48 hours for traffic analytics to populate
Configure these alert policies:
- New App Alert: Trigger when 3+ new apps are detected
- High Risk App Alert: Trigger when apps with risk score above 7 are used by 10+ users
- AI/ML App Alert: Trigger on any AI/ML category app with data transfer above 1MB
What you get:
- Top 50 applications ranked by usage (bytes transferred, number of users, risk score)
- User-level discovery showing who is using what
- AI application detection (ChatGPT, Claude, Gemini, and others)
- Exportable reports suitable for M&A due diligence documentation
Timeline: 48 hours from enablement to full SaaS visibility.
Method 3: Financial Audit (Paid Shadow Apps)
What it reveals: Paid shadow IT – freemium upgrades and corporate card subscriptions.
How to run it:
- Review recurring charges under $100/month on corporate credit cards (this is the typical shadow IT spending pattern)
- Pull corporate credit card statements and search for common SaaS vendor names
- Conduct brief department P&L reviews ask VPs directly: “What subscriptions does your team pay for outside of IT procurement?”
Typical yield: 20–50 paid shadow applications that don’t appear in any IT inventory.
Prioritized Action Plan
| Priority | Method | Time to Results | Coverage | Cost |
|---|---|---|---|---|
| 1 | Entra ID audit (PowerShell) | 30 minutes | 60–80% identity-connected | Free |
| 2 | Defender for Cloud Apps | 48 hours setup | 90%+ total SaaS | E5 license |
| 3 | Financial audit | 2 days | Paid shadow apps | Free |
M&A Shadow IT Discovery Framework
| Phase | Activity | Owner | Timeline |
|---|---|---|---|
| Pre-deal | Conduct technology questionnaires across departments to identify unknown SaaS applications. | M&A Integration Lead | During due diligence |
| Pre-deal | Entra ID application registration audit | CISO / Identity Team | During due diligence |
| Pre-deal | Review financial records and recurring subscriptions to uncover paid shadow IT outside of IT procurement. | CFO / Procurement | During due diligence |
| Pre-deal | Analyze CASB and network traffic logs to detect unsanctioned cloud usage. | Security Operations | During due diligence |
| Post-deal | Non-human identity inventory | Identity & Access Management | Weeks 1–4 post-close |
| Post-deal | Shadow IT risk classification (5 categories above) | IT Director + Stakeholders | Weeks 2–6 post-close |
| Post-deal | Decommission / adopt / migrate decisions per app | CIO + Department Heads | Weeks 4–8 post-close |
| Pre-migration | Shadow IT remediation execution | Migration Program Lead | Before Wave 1 |
| Post-migration | Severed connection validation | IT Operations | 30-day post-migration |
The Organizational Consequences of Getting This Wrong
When shadow IT goes undiscovered in an M&A, the consequences extend beyond the migration project.
Compliance exposure. The acquiring organization inherits responsibility for data processed by the acquired company’s shadow IT. If that data includes customer PII handled in violation of GDPR, HIPAA, or SOX, the liability transfers with the deal. Regulatory fines don’t care whether the acquiring company knew about the shadow tools.
Security incidents. Orphaned non-human identities and unmanaged OAuth connections in the source tenant become attack vectors in the merged environment. The most damaging breaches in post-M&A environments often originate from inherited shadow infrastructure that no one decommissioned because no one knew it existed.
Synergy erosion. When business processes break because shadow integrations were severed during migration, the productivity impact is immediate and visible. Employees in the acquired company experience the merger as a disruption to their work, not an improvement. Executive confidence in the integration erodes. The synergies that justified the deal get delayed by quarters.
Cultural damage. Acquired employees who relied on shadow tools to do their jobs feel that the merger took away functionality without providing alternatives. This perception, that the acquisition made things worse, drives talent attrition at exactly the moment when retaining acquired talent is critical to realizing deal value.
Financial waste. Both organizations carry duplicate shadow SaaS portfolios, many of which overlap. Without discovery and rationalization, the merged entity continues paying for overlapping tools indefinitely, a recurring cost drain that directly reduces the financial returns of the acquisition.
What This Means for Your Migration Plan
Every tenant-to-tenant migration plan assumes a known environment. Shadow IT makes that assumption false. The gap between the environment IT has inventoried and the environment that actually exists determines how many unplanned failures occur during and after migration.
Discovery before the deal closes is the only way to close that gap. The people who built and depend on shadow IT are most available and most cooperative during due diligence and the early post-close period. Once the migration begins and organizational anxiety peaks, that cooperation declines rapidly.
The cost of discovery is measured in weeks and modest tooling investment. The cost of not discovering is measured in compliance violations, security incidents, broken business processes, and integration delays that subtract directly from deal value.
Next step: Run the Entra ID audit described in Method 1 above. If you discover 100+ shadow applications, you’re not alone – that’s typical for enterprises of any significant size. In modern M&A migrations, shadow IT discovery isn’t optional – it’s the foundation everything else depends on. Without it, every other migration workstream operates on incomplete visibility – a condition that almost guarantees surprises during integration.
Further Reading
- Microsoft Learn: Discover and manage Shadow IT — Microsoft Defender for Cloud Apps
- M&A Strategy Insights: The M365 Pre-Deal Due Diligence Problem – Why You’re Pricing What You Can’t See
- Tenant Discovery Playbook: The Data Room You Should Have Asked For – The Specific Artifacts to Request from the Seller